Open-source projects thrive on community participation and collaboration. As a maintainer, how you respond to help requests can make or break the user experience. Here are some key points to implement if you want to ensure you alienate your users.
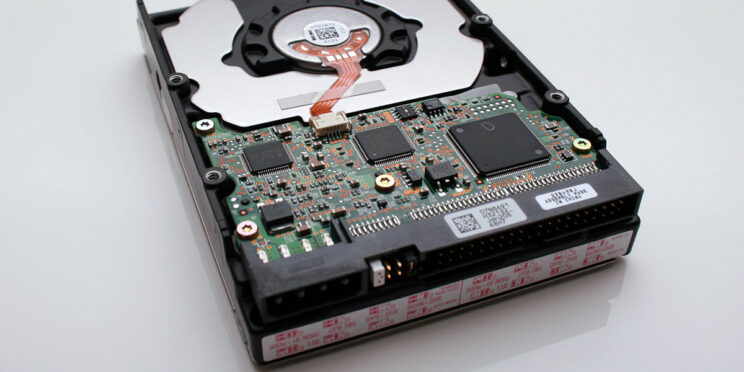
Low-Cost NAS Using GlusterFS
If you’re like me, you’ve found that accessible backup solutions aren’t necessarily the best options. You want to protect your files, expand storage, and provide a platform that can grow with your needs. Today I’m talking about building a low-cost NAS using GlusterFS.
What is a Full-Stack Software Engineer?
You’ve heard the buzzword, you’ve seen the job postings. If so many people are hot about this topic, it must be worth learning about, right? What is a full-stack software engineer anyway?
Unit Testing Auth0 Scripts
You’re a good developer. You like testing your code. Security is important to you, so you also decide that you’ll use a 3rd party service for authentication and choose Auth0. Out-of-the-box, however, doesn’t quite get you what you need so you add some custom rules and scripts to it. You realize, however, that even though these scripts run in a NodeJS instance on their side, they don’t follow conventional patterns. How do I go about unit testing auth0 scripts, you ask yourself?
Skip Authentication Schemes in ASP.NET Core
Authentication in ASP.NET Core is both powerful and dynamic. It provides you the power to incorporate many different schemes and augment the logged-in security principal. Authentication schemes are how we apply authentication in ASP.NET Core. What if you want to skip authentication schemes in favor of another?
Understanding Policy-based authorization in ASP.NET Core
Application security is a vital piece of our overall success as developers. Many of us have learned and applied role-based or claim-based authorization. Overall, this has been “good enough”. Unfortunately, there are still many use-cases it can’t handle gracefully. We call one approach that solves these use-cases policy-based authorization.
SonarQube with GitHub Actions and .NET Core 5.x
GitHub Actions are a great devops tool. As you’re upgrading projects to .NET 5, however, you may run into issues with code coverage and static code analysis. I did. I’ll show you today how to get SonarQube working with GitHub Actions and .NET Core 5.x.
Mixed model binding in ASP.NET Core
While powerful, default model binding in ASP.NET Core handles the basic use-cases. Anything you want to do beyond that — such as mixed model binding — requires a little work to get there.
ASP.NET Core Request Timeout IIS In-Process Mode
Over the years we’ve seen .NET mature and change since v1. We’ve seen server technologies mature in many ways. Things we did yesterday don’t necessarily work the same way today. One of those things that recently struck me was how request timeouts work in IIS. If like me, you just assumed they worked the same in .NET Core then I invite you to join me on this journey. Let’s explore how to make ASP.NET Core request timeouts work properly with IIS in-process hosting mode.
Multiple SSH Keys on GitHub
Recently I ran into an issue I’d never had before. I wanted to access more than one GitHub account from the same machine using SSH. I needed to figure out how to use multiple SSH keys on GitHub from one computer.